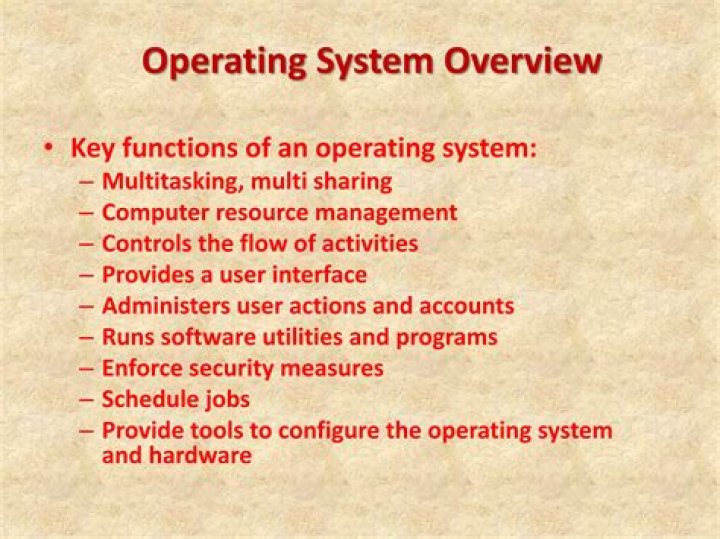
How does an operating system protect itself
Modern hardware has features that allow the OS kernel to protect itself from untrusted user code. An executing stream of instructions and its CPU register context. An execution context for thread(s) that provides an independent name space for addressing some or all of physical memory.
How does operating system protect?
Operating System – The OS must protect itself from security breaches, such as runaway processes ( denial of service ), memory-access violations, stack overflow violations, the launching of programs with excessive privileges, and many others.
Why do operating systems need security?
If a computer program is run by an unauthorized user, then he/she may cause severe damage to computer or data stored in it. So a computer system must be protected against unauthorized access, malicious access to system memory, viruses, worms etc.
How does operating system ensures protection of system data?
OS security encompasses many different techniques and methods which ensure safety from threats and attacks. … Performing regular OS patch updates. Installing updated antivirus engines and software. Scrutinizing all incoming and outgoing network traffic through a firewall.What makes an operating system secure or trustworthy?
Every system can be described by its requirements: statements of what the system should do and how it should do it. An operating system’s security requirements are a set of well-defined, consistent, and implementable rules that have been clearly and unambiguously expressed.
How does the OS protect applications from each other?
In order to protect the execution of individual application jobs from possible interference and attack of other jobs, most contemporary operating systems implement some abstract property of containment, such as process (or task) and TCB (Task Control Block), virtual memory space, file, port, and IPC (Inter Process …
Why the operating system security is important?
Operating systems security plays a primitive role in protecting memory, files, user authentication and data access protection. Consistent protection means that the system meets standard security requirements and have the required functionality to enforce security practices.
How does security affect systems reliability?
Security is the foundation of systems reliability. Security procedures restrict access to only authorized users and protect confidentiality and privacy of sensitive information; provide for processing integrity; and protect against attacks.How do operating systems prevent unauthorized access?
- Hardware firewall – A hardware firewall is a physical device that connects to your network. …
- Software firewall – A software firewall is a software program you install on your computer to helps protect it from unauthorized incoming and outgoing data.
The OS takes raw disk devices and presents users and applications with the abstraction of files and directories with the use of file systems. The OS must manage the disk space used by files and must ensure protection between users by managing which users have access to which files.
Article first time published onWhat technology prevents hackers?
Firewalls. A firewall is a software program or piece of hardware that blocks hackers from entering and using your computer. Hackers search the internet the way some telemarketers automatically dial random phone numbers.
How do I protect my system units?
- Keep up with system and software security updates. …
- Have your wits about you. …
- Enable a firewall. …
- Adjust your browser settings. …
- Install antivirus and anti spyware software. …
- Password protect your software and lock your device. …
- Encrypt your data. …
- Use a VPN.
What are the precautions to be taken in preventing OS security?
- Use strong passwords. …
- Invest in good perimeter defense. …
- Update your software. …
- Shut down services you don’t use. …
- Employ data encryption. …
- Protect your data with backups. …
- Encrypt sensitive communications. …
- Don’t trust foreign networks.
Can a system be reliable but not secure can a system be secure but not reliable?
But at the same time, a safety system must be reliable to be dependable. Thus, when we talk about reliability we must be clear about its context. … There could be systems which are reliable but unsafe, and there could be systems which are safe but unreliable.
What is the difference between system reliability and system safety?
Reliability requirements are concerned with making a system failure-free. Definition: Safety Safety is the probability, that no catastrophic accidents will occur during system operation, over a specified period of time. Safety looks at the consequences and possible accidents.
What is security and reliability?
Reliability is concerned with internal aspects of well-functioning, while security deals with the external aspects that are represented by undesirable events. Reliability will be ensured if every component of the system is reliable and works in optimal security conditions.
What is system protection?
System Protection is a feature available in all Windows 7 editions that helps protect your system and personal files. It takes snapshots, called Restore Points, of your files. You can then later restore these files if a virus, person, or anything else deletes or damages them.
Can a computer be hacked if it is turned off?
In general, the answer is no, you cannot hack into a computer that’s been turned off. Unless two conditions are met, the PC cannot be restarted and hacked from outside, even if you leave it connected to the internet and to power. One of those conditions involve a feature called “Wake on LAN”.
How do you keep your computer secure?
- Back up your data. …
- Use strong passwords. …
- Take care when working remotely. …
- Be wary of suspicious emails. …
- Install anti-virus and malware protection. …
- Don’t leave paperwork or laptops unattended. …
- Make sure your Wi-Fi is secure.
Can someone hack my bank account with my phone number?
Your phone number can be used to reset your account if you forget your password. … With your phone number, a hacker can start hijacking your accounts one by one by having a password reset sent to your phone. They can trick automated systems — like your bank — into thinking they’re you when you call customer service.
What computer protection do I need?
The best way to guard against malware is to install antivirus software, such as Bitdefender, Norton, or Kaspersky. Antivirus software helps to prevent malware from being installed, and it can also remove malware from your computer.
How do firewalls protect your work and personal computers?
A firewall can help protect your computer and data by managing your network traffic. It does this by blocking unsolicited and unwanted incoming network traffic. A firewall validates access by assessing this incoming traffic for anything malicious like hackers and malware that could infect your computer.
What are used in some operating systems to implement protection of the system resources?
In general, commercial operating systems use discretionary access control (DAC) with access control list (ACL) implementation to provide protection to system resources. Among these are most MS Windows operating systems (XP, NT, etc.) and UNIX/LINUX varieties.
Why ensuring system reliability is not a guarantee of system safety?
Ensuring system reliability does not necessarily lead to system safety as reliability is concerned with meeting the system specification (the system ‘shall’) whereas safety is concerned with excluding the possibility of dangerous behavior (the system ‘shall not’).
What is the difference between system safety and industrial safety?
Occupational SafetyProcess SafetyFocuses on changing behaviorFocuses on changing systems
Why would a programmer need to ensure that the system is dependable?
For many computer-based systems, the most important system property is the dependability of the system. The dependability of a system reflects the user’s degree of trust in that system. It reflects the extent of the user’s confidence that it will operate as users expect and that it will not ‘fail’ in normal use.