Is firewall IDS or IPS
A firewall is an intrusion detection mechanism. Firewalls are specific to an organization’s security policy.
Is a firewall an IDS?
A firewall is an intrusion detection mechanism. Firewalls are specific to an organization’s security policy.
Is IPS part of the firewall?
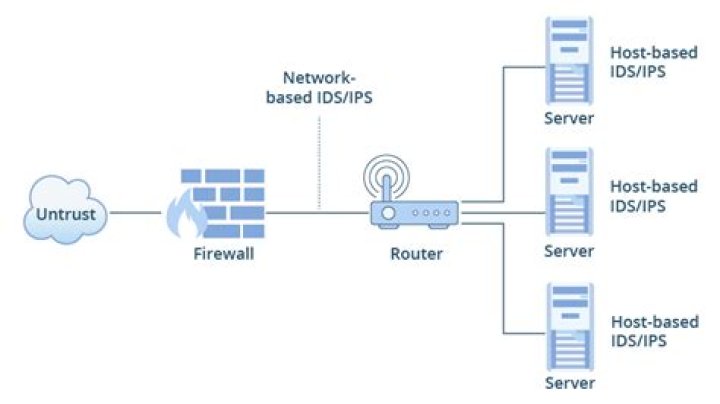
Intrusion Prevention Systems (IPS): live in the same area of the network as a firewall, between the outside world and the internal network. IPS proactively deny network traffic based on a security profile if that packet represents a known security threat.
Is a firewall an IPS or IDS?
The main difference being that firewall performs actions such as blocking and filtering of traffic while an IPS/IDS detects and alert a system administrator or prevent the attack as per configuration. A firewall allows traffic based on a set of rules configured.What is the difference between an IDS and a firewall?
A firewall is a hardware and/or software which functions in a networked environment to block unauthorized access while permitting authorized communications. … A firewall can block connection, while a Intrusion Detection System (IDS) cannot block connection.
What is IPS in networking?
An intrusion prevention system (IPS) is a network security tool (which can be a hardware device or software) that continuously monitors a network for malicious activity and takes action to prevent it, including reporting, blocking, or dropping it, when it does occur.
What is IDS and IPS?
Intrusion prevention is the process of performing intrusion detection and then stopping the detected incidents. These security measures are available as intrusion detection systems (IDS) and intrusion prevention systems (IPS), which become part of your network to detect and stop potential incidents.
What are the 3 types of firewalls?
There are three basic types of firewalls that are used by companies to protect their data & devices to keep destructive elements out of network, viz. Packet Filters, Stateful Inspection and Proxy Server Firewalls. Let us give you a brief introduction about each of these.Is a firewall?
A firewall is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules. … A firewall can be hardware, software, or both.
What is types of firewall?- packet filtering firewall.
- circuit-level gateway.
- application-level gateway (aka proxy firewall)
- stateful inspection firewall.
- next-generation firewall (NGFW)
What is firewall IPS?
An intrusion prevention system (IPS) is a form of network security that works to detect and prevent identified threats. … The IPS reports these events to system administrators and takes preventative action, such as closing access points and configuring firewalls to prevent future attacks.
What can IDS detect?
Signature-based IDS detects the attacks on the basis of the specific patterns such as number of bytes or number of 1’s or number of 0’s in the network traffic. It also detects on the basis of the already known malicious instruction sequence that is used by the malware.
Where is an IDS IPS located on a network?
An intrusion prevention system (IPS) usually sits directly behind the firewall, adding another layer of analysis that removes dangerous contents from the data flow.
Is splunk an IPS?
Splunk is a network traffic analyzer that has intrusion detection and IPS capabilities. There are four editions of Splunk: Splunk Free.
Is IDS and IPS are same?
Intrusion Detection System: An IDS is designed to detect a potential incident, generate an alert, and do nothing to prevent the incident from occurring. … Intrusion Prevention System: An IPS, on the other hand, is designed to take action to block anything that it believes to be a threat to the protected system.
Do I need IDS IPS?
The main difference is that an IDS only monitors traffic. If an attack is detected, the IDS reports the attack, but it is then up to the administrator to take action. That’s why having both an IDS and IPS system is critical.
Is Snort an IDS or IPS?
SNORT is a powerful open-source intrusion detection system (IDS) and intrusion prevention system (IPS) that provides real-time network traffic analysis and data packet logging.
What is IDS and IPS Geeksforgeeks?
Intrusion Prevention System is also known as Intrusion Detection and Prevention System. It is a network security application that monitors network or system activities for malicious activity.
What are the different types of IDS and IPS systems?
- Network-based intrusion detection system (NIPS, IDS IPS)
- Network behavior analysis (NBA)
- Wireless intrusion prevention system (WIPS)
- Host-based intrusion prevention system (HIPS)
Which of these is not a type of firewall?
4. Which of the following is not a software firewall? Explanation: Windows Firewall, Outpost Firewall Pro and Endian Firewall are software firewalls that are installed in the system. Linksys firewall is not an example of a software firewall.
Why is firewall used?
Firewalls provide protection against outside cyber attackers by shielding your computer or network from malicious or unnecessary network traffic. Firewalls can also prevent malicious software from accessing a computer or network via the internet.
Do I have a firewall?
Click Start,Settings, Control Panel, Add/ Remove Programs, and then look for Internet Security or Firewall Software. Click Start, Run. Type “services. … Look for Internet Security or Firewall Software in the services list.
What is the role of firewall?
A firewall is a security firmware or software that forms a barrier between networks to allow and block certain traffic. It inspects traffic so that it can block threats that might harm your systems. Firewalls are designed to authorize low-risk traffic that might not harm your network.
Is a firewall hardware or software?
A firewall is a security device in the form of computer hardware or software. It can help protect your network by acting as an intermediary between your internal network and outside traffic. It monitors attempts to gain access to your operating system and blocks unwanted incoming traffic and unrecognized sources.
Is firewall a protocol?
Most traffic which reaches on the firewall is one of these three major Transport Layer protocols- TCP, UDP or ICMP. All these types have a source address and destination address. Also, TCP and UDP have port numbers. ICMP uses type code instead of port number which identifies purpose of that packet.
Is a gateway a firewall?
The most simple difference between a gateway and a firewall is that a gateway is only hardware, while a firewall can be either hardware or software. 2. A gateway is used to link two separate networks together, allowing users to communicate across several networks.
What are the 4 types of firewalls?
- Packet filtering firewalls. Packet filtering firewalls are the oldest, most basic type of firewalls. …
- Circuit-level gateways. …
- Stateful inspection firewalls. …
- Application-level gateways (proxy firewalls)
Is firewall a virus?
Firewall virus protection observes traffic in the network thereby inhibiting malicious data from entering the network hence thwarting viruses. However, the virus can enter your computer through a spam link, download, or from a flash drive.
What are the 2 types of firewalls?
- Packet-filtering firewalls.
- Proxy firewalls.
- NAT firewalls.
- Web application firewalls.
- Next-gen firewalls (NGFW)
Can IPS prevent DDoS?
Typical IPS devices also claim some anti- DDoS protection. While it is true they can (and do) incorporate some basic protection, the majority of current IPS products evolved from software-based solutions that were signature-based.
Can IDS detect malware?
An IDS is either a hardware device or software application that uses known intrusion signatures to detect and analyze both inbound and outbound network traffic for abnormal activities. This is done through: System file comparisons against malware signatures. Scanning processes that detect signs of harmful patterns.