Should I encrypt my database
Encrypting an entire database should be done with caution since it can result in a serious performance impact. It is therefore wise to encrypt only individual fields or tables. Encrypting data-at-rest protects the data from physical theft of hard drives or unauthorized file storage access.
When should you encrypt database?
Encryption is great for when data is in storage or in transit, but there is one other situation that bears discussion; when your encrypted document is in use. That is to say, when you have opened up that protected document and are looking at it or editing it.
Should I encrypt names in database?
From a privacy and data security point of view, storing an email address encrypted is the best solution. … Storing a key on the server is less secure, but if an attacker has access to the server and is able to read that key, you probably have bigger problems than just decrypted emails.
Should user data be encrypted?
When storing or transmitting personal data, you should use encryption and ensure that your encryption solution meets current standards. You should be aware of the residual risks of encryption, and have steps in place to address these.Can you encrypt data in a database?
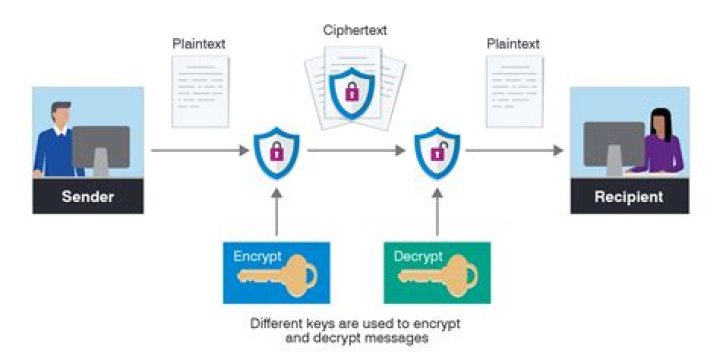
With database encryption, an encryption algorithm transforms data within a database from a readable state into a ciphertext of unreadable characters. With a key generated by the algorithm, a user can decrypt the data and retrieve the usable information as needed.
What are the advantages of encryption?
- Encryption protects your privacy. …
- Encryption prevents Identity Theft and Ransomware Blackmail. …
- Encryption allows you to securly share your files. …
- Encryption protects Lost/Stolen Devices. …
- What to Look For in a File Encryption Solution.
What are the disadvantages to database encryption?
What are the disadvantages to database encryption? Database encryption is complex in order to provide security keys to selected portions of the DB to authorized users/apps. Searching is more inflexible when parts are encrypted. List three cloud service models.
What is the purpose of encryption?
Encryption enhances the security of a message or file by scrambling the content. To encrypt a message, you need the right key, and you need the right key to decrypt it as well.It is the most effective way to hide communication via encoded information where the sender and the recipient hold the key to decipher data.What happens to your data when it is encrypted?
What happens to your data when it is encrypted? It is transferred to a third party, encoded, then sent back. It is compressed, renamed, and archived. It is sent through a series of supercomputers to be compressed multiple times.
Is encryption a legal requirement?National legislation establishes a general right for individuals to use encryption products and services. … National legislation or policy provides for state authorities to be able to require individuals to decrypt (or assist in the decryption) of encrypted communications.
Article first time published onShould you encrypt all emails?
When encrypting emails, it’s important to encrypt all of them, not just the ones with sensitive information. If only some of your emails are encrypted, it is a red flag for a hacker and could make your inbox even less secure.
Should emails be hashed?
So the simple answer is: do not communicate email addresses or passwords, nor hashes of them, to third parties. If you accidentally leak even hashes, this is a privacy breach. When you share data, use meaningless identifiers for user accounts, for example sequential IDs or random UUIDs.
Does database encryption affect performance?
TDE has an estimated performance impact around 3-5% and can be much lower if most of the data accessed is stored in memory. The impact will mainly be on the CPU, I/O will have a smaller impact. See the SQL documentation on this topic for more details.
Is SQL encrypted at rest?
Transparent Data Encryption (TDE) encrypts SQL Server, Azure SQL Database, and Azure Synapse Analytics data files. This encryption is known as encrypting data at rest. To help secure a database, you can take precautions like: Designing a secure system.
Are Microsoft SQL databases encrypted?
Since SQL Server 2008 Enterprise and SQL Server 2019 Standard, Microsoft has supported automatic encryption with TDE and column-level encryption for Enterprise Edition users and above. … You might have a SQL Server database, but not be using Microsoft programming languages.
What is the major issue with database encryption?
Disadvantages of application-level encryption In addition, application-level encryption may have a limiting effect on database performance. If all data on a database is encrypted by a multitude of different applications then it becomes impossible to index or search data on the database.
How safe is encrypted data?
Generally, encryption is safe. Data transmitted and stored with encryption is safer than when left unencrypted. The average user uses encryption automatically many times a day when using a web browser or mobile app. Manual file encryption is safe with responsible handling of the decryption keys.
Why encryption is not widely used?
Decision-makers and executives withhold their support for encryption for a wide range of reasons. A large portion of executives don’t want their data encrypted because they view encryption as being too complicated to use. Many think encryption will slow them, and/or their systems, down too much.
Why do hackers use encryption?
Encrypting data is used as a security measure to protect sensitive data from being accessed by parties that do not have the right to access it, such as malicious parties or those who might use the data for underhand and nefarious means.
Why do companies use data encryption?
The encryption of data in companies prevents information leaks and mitigates the cost of its impact. It is one of the best security solutions to protect sensitive information, but you must know what documents to encrypt and how to implement it effectively.
What does encryption protect against?
How does encryption work? Encryption is the process of taking plain text, like a text message or email, and scrambling it into an unreadable format — called “cipher text.” This helps protect the confidentiality of digital data either stored on computer systems or transmitted through a network like the internet.
What does 256 bit encryption mean?
256-bit encryption is refers to the length of the encryption key used to encrypt a data stream or file. A hacker or cracker will require 2256 different combinations to break a 256-bit encrypted message, which is virtually impossible to be broken by even the fastest computers.
Is encrypted data still personal data?
If under the GDPR, encrypted data is regarded as personal data, thus subjecting any businesses that process the data to regulation and potential liability, it will hamper the growth of the digital economy.
Do I need to encrypt data for GDPR?
Although there are no explicit GDPR encryption requirements, the regulation does require you to enforce security measures and safeguards. The GDPR repeatedly highlights encryption and pseudonymization as “appropriate technical and organizational measures” of personal data security.
Is encryption a computer crime?
Cyber criminals encrypt communication and the stored files of their activities. Law enforcement agencies cannot usually obtain wiretaps for a criminal’s phone, so encryption often keeps the secrets of cyber criminals safe. Public safety is at risk when criminals including terrorists encrypt communication.
What happens if I encrypt an email?
Encrypting an email message in Outlook means it’s converted from readable plain text into scrambled cipher text. Only the recipient who has the private key that matches the public key used to encrypt the message can decipher the message for reading.
Should a company encrypt their email traffic?
E-mail encryption is important especially when sending confidential information. People want to use electronic communication tools also when communicating confidential matters, such as personal data, contract papers, company business secrets and sending different passwords to other parties.
Is Gmail encrypted?
Gmail is capable of encrypting the email it sends and receives, but only when the other email provider supports TLS encryption. In other words, encrypting 100% of all email on the Internet requires the cooperation of all online mail providers.
Should emails be stored in plain text?
10 Answers. If you’re going to need the email address in the future, then you’ll have to store them in plain text. You could encrypt them, of course, however, this is effectively security through obscurity in this case. Basically, if your application’s perimeter is secure, your data within it can be plain text.
Is hashed email PII?
No. So long as you discard the plaintext after hashing it, the hash is not personally identifying and can’t be reversed or cross referenced to reveal the original email address.
What is a hashed email file?
What is a Hashed Email? A hashed email is a cryptographic function. Hashing is a way of encrypting a piece of data, like an email address, into a hexadecimal string. Each email has its own unique hexadecimal string that remains consistent no matter where the email is used as a login.