What are the functions of authentication and encryption in GSM
GSM has its security methods standardized. GSM maintains end-to-end security by retaining the confidentiality of calls and anonymity of the GSM subscriber. Temporary identification numbers are assigned to the subscriber’s number to maintain the privacy of the user.
What are the functions of authentication and encryption in GSM in mobile computing?
GSM has its security methods standardized. GSM maintains end-to-end security by retaining the confidentiality of calls and anonymity of the GSM subscriber. Temporary identification numbers are assigned to the subscriber’s number to maintain the privacy of the user.
What is GSM authentication?
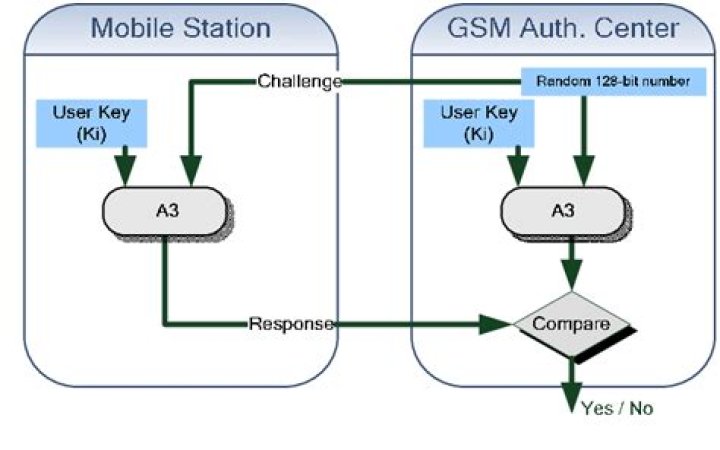
Authentication in the GSM system is achieved by the Base Station sending out a challenge to the mobile station. The MS uses a key stored on its SIM to send back a response that is then verified. This only authenticates the MS, not the user. Figure 15: process of authentication in GSM.
What is GSM encryption?
GSM encryption is the means by which phone conversations on networks using GSM are scrambled, such that they cannot be descrambled and intercepted by others. Due to their potential uses by terrorist and hostile nations, intelligence agencies in the West are concerned about the dangers inherent in exporting such codes.Which is authentication algorithm in GSM?
The A3 ciphering algorithm is used to authenticate each mobile by verifying the user password within the SIM with the cryptographic key at the MSC. The A5 ciphering algorithm is used for encryption.
What is call routing in GSM?
In a mobile system the endpoints of the connection may not be fixed. A GSM subscriber may roam nationally as well as internationally. The VLR allocates a MSRN from an associated pool to the call and creates a binding between the called subscribers IMSI and the MSRN. …
What is A8 algorithm in GSM?
The COMP128 algorithms are implementations of the A3 and A8 functions defined in the GSM standard. A3 is used to authenticate the mobile station to the network. A8 is used to generate the session key used by A5 to encrypt the data transmitted between the mobile station and the BTS.
What is A8 algorithm?
Ciphering Key Generating Algorithm A8. This algorithm is used in conjunction with Ki , the authentication key, and RAND (Random Number) to generate Kc (Cipher Key). This is used with A5/X to cipher the data stream between the MS (Mobile Station) and the GSM network.How does cellular authentication work?
based digital cellular networks that are based on GSM technology (although they may appear under a different name). … The basic approach to authentication is a challenge response method whereby the network sends a random value and the phone has to encrypt it with its secret key and send it back for verification.
What is A3 A5 A8 algorithm in GSM?Three security algorithms are documented in GSM specifications for this purpose. They are called A3, A5 and A8. A3 is authentication algorithm, A8 is ciphering key generating algorithm and A5 is a stream cipher for encryption of user data transmitted between mobile and base station.
Article first time published onWhat are the advantages of GSM?
- More suitable network with robust features.
- No roaming charges on International calls.
- Worldwide connectivity and extensive coverage.
- SAIC and DAIC techniques used in GSM provide very high transmission quality.
How does authentication center AuC work in GSM?
The authentication center (AuC) is a key component of a global system for mobile communications (GSM) home locator register (HLR). The AuC validates any security information management (SIM) card attempting network connection when a phone has a live network signal.
What are the security services offered by GSM?
We may therefore say that GSM provides three security services: • temporary identities for the confidentiality of the user identity; • authentication for the corroboration of the identity of the user; • enciphering for the confidentiality of user-related data.
How many encryption algorithms are there?
There are two types of encryption algorithms, each with its own variations in terms of how it’s put into practice. This blog post will highlight the most important implementations of each algorithm. Time to learn how encryption protects your sensitive personal and company data.
What is GSM explain the architecture of GSM?
The GSM architecture consists of three major interconnected subsystems that interact with themselves and with users through certain network interface. The subsystems are Base Station Subsystem (BSS), Network Switching Subsystem (NSS) and Operational Support Subsystem (OSS).
Where is IMSI stored?
The IMSI is stored in the Subscriber Identity Module (SIM) inside mobile devices and is sent by the mobile device to the appropriate network in which the SIM is associated.
Which identifier provides a temporary address that hides the identity and location of the subscriber?
Temporary Mobile Subscriber Identity (TMSI) can be assigned by the VLR, which is responsible for the current location of a subscriber.
Which guidelines follows GSM?
Explanation: GSM services follow ISDN guidelines and are classified as either teleservices or data services. Teleservices include standard mobile telephony and mobile originated or base originated traffic.
What mechanism does GSM use?
GSM makes use of narrowband Time Division Multiple Access (TDMA) technique for transmitting signals. GSM was developed using digital technology. It has an ability to carry 64 kbps to 120 Mbps of data rates. Presently GSM supports more than one billion mobile subscribers in more than 210 countries throughout the world.
What are the different types of GSM call?
- Voice Calls. The most basic Teleservice supported by GSM is telephony. …
- Videotext and Facsmile. Another group of teleservices includes Videotext access, Teletex transmission, Facsmile alternate speech and Facsmile Group 3, Automatic Facsmile Group, 3 etc.
- Short Text Messages.
What is the role of authentication center?
The authentication center (AuC) is a function to authenticate each SIM card that attempts to connect to the gsm core network (typically when the phone is powered on). Once the authentication is successful, the HLR is allowed to manage the SIM and services described above.
Why does GSM separate the MS and SIM?
Why does GSM separate the MS and SIM? – Quora. Because in Europe where most of the standards for GSM were originally from (the USA was focused at the time on AMPS and IS-136/CDMA), they didn’t have devices tied to the contract like the USA markets did.
What is SIM based authentication?
SIM-based authentication is a powerful tool for achieving these goals. This is the method whereby mobile/cellular devices that have a SIM card use the same SIM card to authenticate the device for the Wi-Fi service. Users will just securely fly on to the Wi-Fi network.
What are the 3 important features of GSM security?
GSM security issues Length of Kc (cipher key) is 64 bits only which is inadequate. GSM mobile can not authenticate the network (BTS) but reverse is possible. Integrity protection is not implemented. ciphering algorithms are not available for public and was managed only by GSMA.
What is the use of ciphering?
Ciphers, also called encryption algorithms, are systems for encrypting and decrypting data. A cipher converts the original message, called plaintext, into ciphertext using a key to determine how it is done.
What is the function of GSM module?
A customised Global System for Mobile communication (GSM) module is designed for wireless radiation monitoring through Short Messaging Service (SMS). This module is able to receive serial data from radiation monitoring devices such as survey meter or area monitor and transmit the data as text SMS to a host server.
What is difference between GSM and CDMA?
The basic difference between GSM and CDMA is that the GSM is a SIM specific i.e. a mobile phone is identified in the network by the removable SIM inserted in that phone. … On the other hands, CDMA uses EVDO which provide higher data bandwidth hence it has faster data transmission rate.
How is GSM handover done?
- Old and new BTSs synchronised: In this case the mobile is given details of the new physical channel in the neighbouring cell and handed directly over. …
- Time offset between synchronised old and new BTS: In some instances there may be a time offset between the old and new BTS.
What is the function of MSC in GSM?
Mobile Switching Centre A Mobile Switching Center (MSC) is a core part of the GSM/CDMA network system. It acts as a control center of a Network Switching Subsystem (NSS). The MSC connects calls between subscribers by switching the digital voice packets between network paths.
What is the role of AUC in GSM network?
The Authentication Centre (AUC) is a function in a GSM network used for the authentication a mobile subscriber that wants to be connected to the network. … Once the subscriber is authenticated, the AUC is responsible for the generation of the parameters used for the privacy and the ciphering of the radio link.
What is the difference between VLR and HLR?
In general, HLR contains information about all subscribers within a network, while VLR contains more dynamic information relevant to subscribers roaming within the VLR area. HLR acts as a fixed reference point for a particular mobile station (subscriber), while its VLR can vary depending on mobility and network design.