What does a SIEM tool do
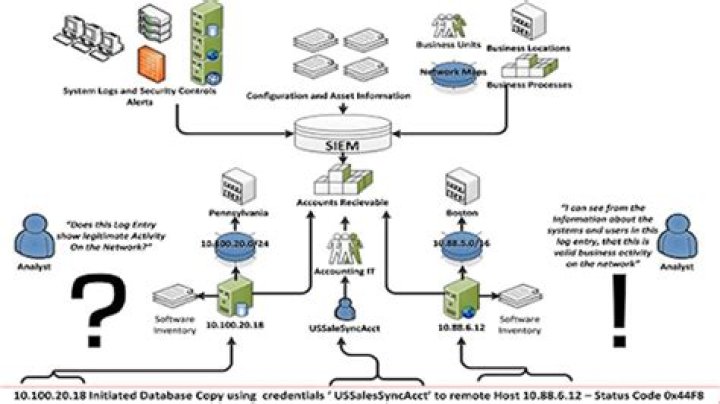
SIEM software combines security information management (SIM) and security event management (SEM) to provide real-time analysis of security alerts generated by applications and network hardware.
What is SIEM used to assist with?
Security Information and Event Management (SIEM) is a term coined by Gartner in 2005 to describe technology used to monitor and help manage user and service privileges, directory services and other system configuration changes; as well as providing log auditing and review and incident response.
What are some examples of SIEM?
- SolarWinds Security Event Manager.
- Micro Focus ArcSight ESM.
- SolarWinds Threat Monitor.
- Splunk Enterprise Security.
- LogRhythm NextGen SIEM.
- IBM QRadar.
- AlienVault Unified Security Management.
- Sumo Logic.
What does SIEM?
SIEM stands for security, information, and event management. SIEM technology aggregates log data, security alerts, and events into a centralized platform to provide real-time analysis for security monitoring.What can I monitor with SIEM?
What should I log in a SIEM? You’ll want the logs from the critical components of your network and business. You will want the logs from your firewall for sure. You will also want logs from your key servers, especially your Active Directory server and your key application and database servers.
Is Kibana a SIEM?
At the heart of Elastic SIEM is the new SIEM app, an interactive workspace for security teams to triage events and perform initial investigations. … Kibana has always been a wonderful place for security teams to visualize, search, and filter their security data.
What is SIEM tool in security?
Security Information and Event Management (SIEM) is a set of tools and services offering a holistic view of an organization’s information security. SIEM tools provide: Real-time visibility across an organization’s information security systems. Event log management that consolidates data from numerous sources.
Is a SIEM necessary?
Intrusion detection and prevention systems (IDS/IPS) alone won’t be able to detect or prevent malware like this, which is why a SIEM is so essential. Additionally, SIEM solutions are able to aggregate data from across your entire network and analyze this data together to limit false positives.What is the best SIEM tool?
- Datadog Security Monitoring EDITOR’S CHOICE.
- SolarWinds (FREE TRIAL)
- ManageEngine (FREE TRIAL)
- Splunk.
- OSSEC.
- LogRhythm.
- AT&T Cybersecurity.
- RSA.
Security Information and Event Management (SIEM) is a software solution that aggregates and analyzes activity from many different resources across your entire IT infrastructure. SIEM collects security data from network devices, servers, domain controllers, and more.
Article first time published onIs Nessus a SIEM?
Nessus is just one part of an overall software package called Security Center CV (Continuous View). … However, Tenable doesn’t like referring to any of this as a Security Information and Event Management (SIEM) tool.
Is zscaler a SIEM tool?
Zscaler and SIEM and Analytics. … By using NSS, Zscaler customers can send weblog data to the SIEM to facilitate log correlation from multiple sources, thus allowing organizations to analyze traffic patterns across their entire networks.
How does SIEM collect data?
The SIEM can collect data in four ways: Via an agent installed on the device (the most common method) By directly connecting to the device using a network protocol or API call. By accessing log files directly from storage, typically in Syslog format.
What is SIEM alerting?
A SIEM alert is a tool most commonly used by SOCs to protect an organization. … SIEM tools analyze the state of the processes that are occurring on the IT system and classify thousands of events to evaluate their behavior and detect possible anomalies that could lead to a cyberattack.
What are SIEM best practices?
- Start slow. The most common mistake MSPs make regarding SIEM implementation is trying to do too much too soon. …
- Think about compliance requirements. …
- Adjust correlation rules. …
- Collect security log data efficiently. …
- Have a plan after IT threat detection.
What is McAfee SIEM?
McAfee SIEM solutions bring event, threat, and risk data together to provide the strong security insights, rapid incident response, seamless log management, and compliance reporting required for more efficient and effective security operations.
What is SIEM and SOC?
SIEM stands for Security Incident Event Management and is different from SOC, as it is a system that collects and analyzes aggregated log data. SOC stands for Security Operations Center and consists of people, processes and technology designed to deal with security events picked up from the SIEM log analysis.
How does QRadar SIEM work?
The core functionality of QRadar SIEM is focused on event data collection, and flow collection. … QRadar translates or normalizes raw data in to IP addresses, ports, byte and packet counts, and other information into flow records, which effectively represents a session between two hosts.
Is Elk a SIEM tool?
The answer to this question is simple. In its raw form, consisting of Logstash, Elasticsearch, Kibana, and Beats — the ELK Stack is NOT a SIEM solution. While an extremely powerful tool for centralized logging, the ELK Stack cannot be used as-is for SIEM.
What is IBM radar?
IBM QRadar is an enterprise security information and event management (SIEM) product. It collects log data from an enterprise, its network devices, host assets and operating systems, applications, vulnerabilities, and user activities and behaviors.
What is Elasticsearch Siem?
Elastic Security equips security teams to stop threats quickly and at cloud scale, with the best-in-class platform for prevention, detection, and response. Start free trial. 14-day free trial, no credit card required. Experience the fast, scalable Elastic SIEM on Elasticsearch Service.
Is Wireshark a SIEM tool?
A final word on what Wireshark is not. It is not a security information and event management (SIEM) suite nor should it be “sold” to management as such. It is no substitute for a SIEM, although its data can be used for some of the same activities, such as event correlation and forensic packet analysis.
Is Darktrace a SIEM?
Rather than centralizing data and alerts or relying on retrospective detection methods as a SIEM does, Darktrace offers intelligent, automatic threat detection and response, powered by self-learning AI that can catch every threat – from stealthy insiders to zero-day malware.
How good is azure Sentinel?
“A Wonderful SIEM/SOAR Experience from Microsoft” As a new product, Azure sentinel was easy to learn and use. It was very easy to configure Microsoft data sources to Azure sentinel. Log analytic rules are easy to edit. It’s cost effective compared to other commercial products in the market.
Who needs SIEM?
Regulatory Compliance Companies that use SIEM can protect their sensitive data and establish proof that allows them to touch compliance requirements. A SIEM server receives log data from several sources and can create one report that addresses all of the logged security events among these sources.
How many companies use SIEM?
CompanyEze Castle Integration, Inc.CountryUnited StatesRevenue50M-100MCompany Size200-500CompanyGartner, Inc.
What makes a SIEM so powerful on a network?
A SIEM solution detects incidents that otherwise can go unnoticed. This technology analyzes the log entries to detect indicators of malicious activity. Moreover, since it gathers events from all sources across the network, the system can reconstruct the attack timeline to help determine its nature and impact.
What is the most used SIEM?
- Comparison of the Top SIEM Software.
- #1) SolarWinds SIEM Security and Monitoring.
- #2) Datadog.
- #3) Splunk Enterprise SIEM.
- #4) McAfee ESM.
- #5) Micro Focus ArcSight.
- #6) LogRhythm.
- #7) AlienVault USM.
WHY is SIEM pronounced SIM?
Security information and event management (SIEM) is an approach to security management that combines SIM (security information management) and SEM (security event management) functions into one security management system. The acronym SIEM is pronounced “sim” with a silent e.
Is SIEM a vulnerability management?
SIEM—or Security Information and Event Management—are solutions that monitor an organization’s IT environment, relaying actionable intelligence and enabling security teams to manage potential vulnerabilities proactively.
Is tenable io a SIEM?
A critical component of Tenable’s USM platform, Tenable’s LCE provides advanced and unique SIEM functionality. By combining normalized log data from devices throughout enterprise networks with vulnerability intelligence, it detects botnets and other malicious communications that other solutions miss.