What is a connect scan
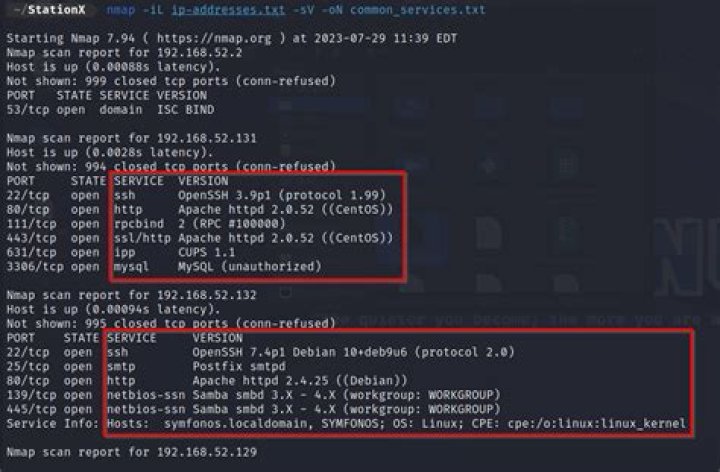
TCP connect scanning commonly involves establishing a full connection, and then subsequently tearing it down, and therefore involves sending a significant number of packets to each port that is scanned. Compared to other types of scans, a TCP Connect scan is slow and methodical.
How is the connect scan different than the SYN scan?
So the difference between these two scan types is TCP Connect scan establish a full connection with the target but SYN scan completes only a half of the connection with target.
What are the 3 types of network scanning?
- Port Scanning – Detecting open ports and running services on the target host.
- Network Scanning – Discovering IP addresses, operating systems, topology, etc.
- Vulnerability Scanning – Scanning to gather information about known vulnerabilities in a target.
What does a SYN scan do?
SYN scanning is a tactic that a malicious hacker can use to determine the state of a communications port without establishing a full connection. This approach, one of the oldest in the repertoire of hackers, is sometimes used to perform a denial-of-service (DoS) attack. SYN scanning is also known as half-open scanning.How do I prevent port scan attacks?
Install a Firewall: A firewall can help prevent unauthorized access to your private network. It controls the ports that are exposed and their visibility. Firewalls can also detect a port scan in progress and shut them down.
What is the principle behind TCP connect scan in Nmap?
1 point 5) What is the basic principle behind TCP Connect Scan in NMAP? a. The scanner machine tries to complete a TCP connection on some port with the target using 3-way handshake to conclude that the port is open.
Which type of Nmap scan is the most reliable?
Explanation: The TCP full connect (-sT) scan is the most reliable.
What is aggressive scan in Nmap?
Aggressive Scanning Nmap has an aggressive mode that enables OS detection, version detection, script scanning, and traceroute. … However, an aggressive scan also sends out more probes, and it is more likely to be detected during security audits.What does Nmap scan do?
Using Nmap Nmap allows you to scan your network and discover not only everything connected to it, but also a wide variety of information about what’s connected, what services each host is operating, and so on. It allows a large number of scanning techniques, such as UDP, TCP connect (), TCP SYN (half-open), and FTP.
How does Nmap scan work?Nmap works by checking a network for hosts and services. Once found, the software platform sends information to those hosts and services which then respond. Nmap reads and interprets the response that comes back and uses the information to create a map of the network.
Article first time published onHow do I do a network scan?
- Open the command prompt.
- Enter the command “ipconfig” for Mac or “ifconfig” on Linux. …
- Next, input the command “arp -a”. …
- Optional: Input the command “ping -t”.
What are the four steps involved in scanning?
- Scope Out The Project. When starting a scanning project the most important thing you can do is get the scope of the project. …
- Organize. Organize all of your documents by how you would like them to be scanned. …
- Index the Documents. …
- Pick the Right EDMS.
Is port scanning illegal in the US?
In the U.S., no federal law exists to ban port scanning. … However – while not explicitly illegal – port and vulnerability scanning without permission can get you into trouble: Civil lawsuits – The owner of a scanned system can sue the person who performed the scan.
Why do hackers use port scanning?
A port scan is a common technique hackers use to discover open doors or weak points in a network. A port scan attack helps cyber criminals find open ports and figure out whether they are receiving or sending data. It can also reveal whether active security devices like firewalls are being used by an organization.
What is the importance of port scanning?
Why Is Port Scanning Important? Since port scanning identifies open ports and services available on a network, it is used by security professionals to identify any security vulnerabilities on that particular network.
When running an nmap SYN scan what will be the Nmap result if ports on the target device do not respond?
A SYN/ACK indicates the port is listening (open), while a RST (reset) is indicative of a non-listener. If no response is received after several retransmissions, the port is marked as filtered. The port is also marked filtered if an ICMP unreachable error (type 3, code 0, 1, 2, 3, 9, 10, or 13) is received.
How does a TCP connection work?
TCP organizes data so that it can be transmitted between a server and a client. It guarantees the integrity of the data being communicated over a network. Before it transmits data, TCP establishes a connection between a source and its destination, which it ensures remains live until communication begins.
How do I run a port scan with Nmap?
To get started, download and install Nmap from the nmap.org website and then launch a command prompt. Typing nmap [hostname] or nmap [ip_address] will initiate a default scan. A default scan uses 1000 common TCP ports and has Host Discovery enabled. Host Discovery performs a check to see if the host is online.
Is Nmap illegal?
While civil and (especially) criminal court cases are the nightmare scenario for Nmap users, these are very rare. After all, no United States federal laws explicitly criminalize port scanning. … Unauthorized port scanning, for any reason, is strictly prohibited.
What can be done with Nmap?
- Create a complete computer network map.
- Find remote IP addresses of any hosts.
- Get the OS system and software details.
- Detect open ports on local and remote systems.
- Audit server security standards.
- Find vulnerabilities on remote and local hosts.
Is it safe to use Nmap?
NMap is as safe as about any other well-respected free software. Nothing is totally safe. Even Windows and builds of Linux contain at best occasional vulnerabilities. There might be some restricted environments where it is against some rule to install it, but that’s a matter of policy you would need to check locally.
What does Tcpwrapped mean Nmap?
when Nmap is ran as a non-root user it performs TCP scan for port scan. TCPwrapper is software at host machine which closes the TCP connection after three way handshake, when client has no access to a particular port.
How long do Nmap scans take?
I ran nmap -Pn on all possible addresses for the local network and it took 50 minutes. If I limit the range to 100-200 , for example, the same scan takes 3-4 minutes.
Can Nmap detect Web server details?
Using its nmap-services database of about 2,200 well-known services, Nmap would report that those ports probably correspond to a mail server (SMTP), web server (HTTP), and name server (DNS) respectively. This lookup is usually accurate—the vast majority of daemons listening on TCP port 25 are, in fact, mail servers.
What is the difference between nmap and wireshark?
Wireshark is mostly generic scanning and hence returns details of every request that is made in the network. Nmap allows applications to learn about the other computers that are available on the network. Wireshark allows an application to learn what is being sent or receive on one’s computer.
How do I find out someone's IP address?
1: Use Command Prompt Only thing you need to do is to open the command prompt and on the DOS screen, type “ping” <space> “the address of the website you want to trace” and then hit enter. As an example, if you want to know the IP address for Google, type “ping ” and press enter.
How can I see all devices connected to my network?
To see all of the devices connected to your network, type arp -a in a Command Prompt window. This will show you the allocated IP addresses and the MAC addresses of all connected devices.
How do I find an unknown device on my network?
- Tap the Settings app.
- Tap About Phone or About Device.
- Tap Status or Hardware Information.
- Scroll down to see your Wi-Fi MAC address.
What documents do I need to scan?
- Birth certificates.
- Marriage and divorce certificates.
- Social Security cards.
- Drivers’ licenses.
- Passports.
- Insurance policies (auto, home, life, etc.)
- Health insurance cards.
- Immunization records.
How do you use a scan machine?
- Introduction.
- Connect the scanner to your PC.
- Place the material to be scanned into the scanner, just as though you were using a photocopier. …
- Press the scan button on the scanner, which is the button to acquire a digital image.
- Preview the scan.
- Select the scan area in the scanner software.
How long does it take to scan papers?
consider that an average scan on good/medium quality for a 8.5×11 sheet will take at least 1-2 minutes to scan (longer on higher quality) and you then need to physically remove each piece and rename the files. figure 4 minutes per scan.