What is a vulnerability and risk
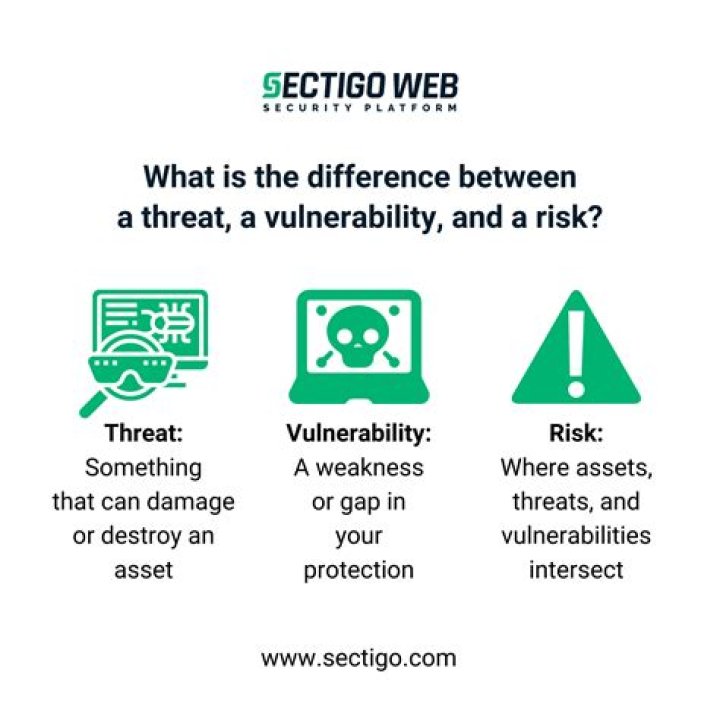
In a nutshell, risk is the potential for loss, damage or destruction of assets or data caused by a cyber threat. … And a vulnerability is a weakness in your infrastructure, networks or applications that potentially exposes you to threats.
What is vulnerability and risk management?
Risk-based vulnerability management (RBVM) is a cybersecurity strategy in which organizations prioritize remediation of software vulnerabilities according to the risk they pose to the organization. A risk-based vulnerability management strategy has several components.
What is risk and vulnerability assessment?
In essence, risk assessment involves looking outside of an organization to determine what threats exist that could potentially lead to problems, while vulnerability assessment involves looking inside the organization for structural flaws and weaknesses.
What is considered a vulnerability?
A vulnerability is a weakness or error in a system or device’s code that, when exploited, can compromise the confidentiality, availability, and integrity of data stored in them through unauthorized access, elevation of privileges, or denial of service.What is vulnerability Owasp?
A vulnerability is a hole or a weakness in the application, which can be a design flaw or an implementation bug, that allows an attacker to cause harm to the stakeholders of an application. Stakeholders include the application owner, application users, and other entities that rely on the application.
What are vulnerabilities in humans?
The standard dictionary definition of vulnerability is to make yourself susceptible to physical or emotional harm, which let’s be honest, sounds a little harsh (read: terrifying). I prefer Brown’s interpretation of it. She explains vulnerability as “uncertainty, risk, and emotional exposure.”
Why being vulnerable is important?
Being vulnerable can help us to work through our emotions easier (rather than pushing them away). Vulnerability fosters good emotional and mental health. Vulnerability also is a sign of courage. We become more resilient and brave when we embrace who we truly are and what we are feeling.
Which of the following is an example of vulnerability?
Other examples of vulnerability include these: A weakness in a firewall that lets hackers get into a computer network. Unlocked doors at businesses, and/or. Lack of security cameras.What are the types of vulnerability?
Types of vulnerability include social, cognitive, environmental, emotional or military. In relation to hazards and disasters, vulnerability is a concept that links the relationship that people have with their environment to social forces and institutions and the cultural values that sustain and contest them.
What are the 3 types of risks?Risk and Types of Risks: Widely, risks can be classified into three types: Business Risk, Non-Business Risk, and Financial Risk.
Article first time published onHow do you assess vulnerability?
A vulnerability assessment is a systematic review of security weaknesses in an information system. It evaluates if the system is susceptible to any known vulnerabilities, assigns severity levels to those vulnerabilities, and recommends remediation or mitigation, if and whenever needed.
What is vulnerability matrix?
The Vulnerability Matrix which is part of WP2 is a conceptual and communicative tool to condense these complex phenomena into a visual summary that flags possible areas for policy action. … The Matrix is intended to support prompt identification of critical and emerging vulnerability elements.
What are the top 10 vulnerabilities?
- Sensitive Data Exposure. …
- XML External Entities. …
- Broken Access Control. …
- Security Misconfiguration. …
- Cross-Site Scripting. …
- Insecure Deserialization. …
- Using Components with Known Vulnerabilities. …
- Insufficient Logging and Monitoring.
How does vulnerability affect hazard risk?
In the context of extensive risk in particular, it is often people’s vulnerability that is the greatest factor in determining their risk. … Vulnerable groups find it hardest to reconstruct their livelihoods following a disaster, and this in turn makes them more vulnerable to the effects of subsequent hazard events.
How many vulnerabilities are there?
1. Over 18,000 vulnerabilities were published in 2020. The NVD database holds 18,362 vulnerabilities published in 2020. This is a higher number than in previous years (17,382 in 2019 and 17,252 in 2018).
Is vulnerability a bad thing?
But, being vulnerable means something else when it’s placed in connection with human flourishing. … “Vulnerability isn’t good or bad. It’s not what we call a dark emotion, nor is it always a light, positive experience. Vulnerability is the core of all emotions and feelings.
How can vulnerable be powerful?
Vulnerability is an act of courage because you merge with your authentic self, instead of hiding behind a facade to appease others. It is within the unknown where your greatest potential lies. … To embrace vulnerability as your greatest strength, you will need to become aware of your pain points.
Is it healthy to be vulnerable?
Vulnerability sounds like truth and feels like courage. … Yet, nothing could be further from the truth. In fact, asking for help is one of the most honest and courageous things we can do for ourselves and the people we care about. And it’s just one of many healthy ways we can choose to be vulnerable.
How can a person be vulnerable?
- Ask for what you need. When we’re hurting, it’s easy to dismiss our pain or try to protect ourselves and the people around us by closing off. …
- Be willing to expose your feelings. …
- Say what you want. …
- Express what you really think. …
- Slow down and be present.
What are your own vulnerabilities?
Your core vulnerability is the emotional state that is most dreadful to you, in reaction to which you’ve developed the strongest defenses. … For most people, either fear (of harm, isolation, deprivation) or shame (of failure) constitutes their core vulnerability. Fear and shame are both pretty dreadful, to be sure.
What are environmental risks?
Environmental risk is the probability and consequence of an unwanted accident. Because of deficiencies in waste management, waste transport, and waste treatment and disposal, several pollutants are released into the environment, which cause serious threats to human health along their way.
What are the five main categories of risk?
They are: governance risks, critical enterprise risks, Board-approval risks, business management risks and emerging risks. These categories are sufficiently broad to apply to every company, regardless of its industry, organizational strategy and unique risks.
What are pure risks?
Pure risk refers to risks that are beyond human control and result in a loss or no loss with no possibility of financial gain. Fires, floods and other natural disasters are categorized as pure risk, as are unforeseen incidents, such as acts of terrorism or untimely deaths.
How do you manage vulnerability?
- Step 1: Identifying Vulnerabilities. …
- Step 2: Evaluating Vulnerabilities. …
- Step 3: Treating Vulnerabilities. …
- Step 4: Reporting vulnerabilities.
What does risk management include?
Risk management is the process of identifying, assessing and controlling threats to an organization’s capital and earnings. These risks stem from a variety of sources including financial uncertainties, legal liabilities, technology issues, strategic management errors, accidents and natural disasters.
What is a synonym for vulnerability?
easiness, gullibility, naïveté (also naivete or naiveté)
What is element at risk?
General introduction to elements-at-risk. Assets – or elements at risk – is a generic term that signifies everything that might be exposed to hazards, ranging from buildings to the economy and from individual persons to communities. … In areas without assets, hazards are not considered as a problem.
What is vulnerability summary?
A vulnerability analysis is a review that focuses on security-relevant issues that either moderately or severely impact the security of the product or system.
What is risk assessment in cyber security?
A cybersecurity risk assessment identifies the various information assets that could be affected by a cyber attack (such as hardware, systems, laptops, customer data, and intellectual property), and then identifies the various risks that could affect those assets.
Which of the following is not a vulnerability?
Which of the following is not physical layer vulnerability? Explanation: Unauthorized network access is not an example of physical layer vulnerability. The rest three – Physical theft of data & hardware, damage or destruction of data & hardware and keystroke & Other Input Logging are physical layer vulnerabilities.
What are the most common vulnerabilities found in Windows 10?
- Microsoft Windows Journal Vulnerability (MS15-098)
- Internet Explorer Vulnerabilities (MS15-079) …
- Microsoft Graphics Component Vulnerabilities (MS15-080) …
- Microsoft Edge Vulnerabilities (MS15-091) …
- Windows 10 Mount Manager Vulnerability (CVE-2015-1769, MS15-085) …