What is CMAC in cryptography
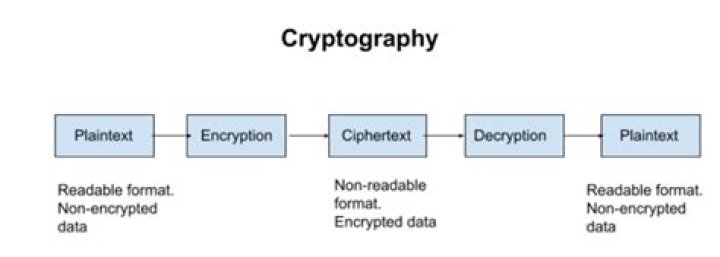
In cryptography, CMAC is a block cipher-based message authentication code algorithm. It may be used to provide assurance of the authenticity and, hence, the integrity of data. This mode of operation fixes security deficiencies of CBC-MAC (CBC-MAC is secure only for fixed-length messages). … CMAC is equivalent to OMAC1.
What is HMAC and CMAC in cryptography?
Well, CMACs (Cipher-based message authentication codes) create message authentication codes (MACs) using a block cipher and a secret key. They differ from HMACs in that they use a block symmetric key method for the MACs rather than a hashing method.
Is MAC and CMAC same?
CMAC is a simple variant of the CBC MAC (Cipher Block Chaining Message Authentication Code). Whereas the basic CBC MAC is only secure on messages of one fixed length (and that length must be a multiple of the block size), CMAC takes and is secure across messages of any bit length.
What is the full form of CMAC in cryptography?
Crypto-material Management and Assistance Centre.How does AES CMAC work?
Cipher-Based Message Authentication Code (AES-CMAC) The core of the CMAC is the previously discussed CBC-MAC. The key difference between these two is that the CMAC works on messages of any bit lengths. The function takes as input a secret key, a message and its length, and returns a 128-bit string which is the MAC.
What is HMAC explain?
In cryptography, an HMAC (sometimes expanded as either keyed-hash message authentication code or hash-based message authentication code) is a specific type of message authentication code (MAC) involving a cryptographic hash function and a secret cryptographic key.
What is HMAC Crypto?
In cryptography, a keyed hash message authentication code (HMAC) is a specific type of message authentication code (MAC) involving a cryptographic hash function(hence the ‘H’) in combination with a secret cryptographic key.
What is the meaning of CMAC in hospital?
Chairman Medical Advisory Committee (CMAC)What is a CMAC in healthcare?
Health Science | AMCA CMAC. The AMCA CMAC exam is an industry certification that measures students’ knowledge and skills needed to become a clinical medical assistant (CMA). When someone passes the exam, they earn a certification designating that they can work in a healthcare facility as a CMA.
Is CBC-Mac collision resistant?This example also shows that a CBC-MAC cannot be used as a collision-resistant one-way function: given a key it is trivial to create a different message which “hashes” to the same tag.
Article first time published onWhat is CMAC on router?
The CM MAC (Cable Modem MAC address) and Serial Number of your cable modem are printed on the bottom label.
How secure is CBC?
AES-CBC vs AES-GCM Although CBC may theoretically have some vulnerabilities, the consensus is that CBC is secure. CBC is, indeed, recommended in the OpenVPN manual. OpenVPN now also supports AES-GCM (Galios/Counter Mode). GCM provides authentication, removing the need for an HMAC SHA hashing function.
What is CBC residue?
The CBC residue is the MAC (message authentication code), or it is sometimes called a MIC (message integrity code). If any bit of the message is changed, the MAC is highly likely to change. The receiver computes the CBC residue and and compares it with the received MAC.
What is Hmac sha256?
Remarks. HMACSHA256 is a type of keyed hash algorithm that is constructed from the SHA-256 hash function and used as a Hash-based Message Authentication Code (HMAC).
What is difference between MAC and HMAC?
The main difference between MAC and HMAC is that MAC is a tag or a piece of information that helps to authenticate a message, while HMAC is a special type of MAC with a cryptographic hash function and a secret cryptographic key. … Furthermore, MAC and HMAC are two codes used in cryptography to pass the messages.
Which algorithm Among was chosen as the AES algorithm?
Which algorithm among- MARS, Blowfish, RC6, Rijndael and Serpent -was chosen as the AES algorithm? Explanation: In October 2000 the Rijndael algorithm was selected as the winner and NIIST officially announced that Rijndael has been chosen as Advanced Encryption Standard (AES) in November 2001. 5.
What is hashing and HMAC?
Hash-based message authentication code (or HMAC) is a cryptographic technique that combines public keys, private keys, and a hash into a mix hackers can’t unpack. Use HMAC, and you’ll tap into a method that can both encrypt data and check the integrity of information you get in return.
What is OpenSSL HMAC?
OpenSSL::HMAC allows computing Hash-based Message Authentication Code (HMAC). It is a type of message authentication code (MAC) involving a hash function in combination with a key. HMAC can be used to verify the integrity of a message as well as the authenticity.
What is keyed and keyless hash function?
Hmac is an algo to make keyless hash into keyed hash. keyed hash example is AES-MAC and keyless example is Sha-1, MD5. HMAC- AES uses key to produce MAC. the MAC is derived by computation using the ipad and opad along with the key and the message . HMAC-AES: MAC(M)=c(t), the last block in cbc mode.
Does https use HMAC?
HTTPS, SFTP, FTPS, and other transfer protocols use HMAC. The cryptographic hash function may be MD-5, SHA-1, or SHA-256. Digital signatures are nearly similar to HMACs i.e they both employ a hash function and a shared key.
What is HMAC SHA1 signature?
HMACSHA1 is a type of keyed hash algorithm that is constructed from the SHA1 hash function and used as an HMAC, or hash-based message authentication code. … An HMAC can be used to determine whether a message sent over an insecure channel has been tampered with, provided that the sender and receiver share a secret key.
Is HMAC symmetric or asymmetric?
The main difference is that digital signatures use asymmetric keys, while HMACs use symmetric keys (no public key).
What is a CMAC rate?
On this page you will find the CHAMPUS Maximum Allowable Charges (CMAC) for the most frequently used procedures or services. These charges are the maximum amounts TRICARE is allowed to pay for each procedure or service and are tied by law to Medicare’s allowable charges.
Does TRICARE follow Medicare fee schedule?
The TRICARE allowable charge is tied by law to Medicare’s allowable charge whenever practical and may vary based on the prevailing rate in a given location.
Who is the CMAC of Oauthc?
Prof. John Foluso OWOTADE, a Honourary Consultant Oral/Maxillofacial Surgery has been appointed the new Chairman, Medical Advisory Committee (CMAC) Obafemi Awolwo University Teaching Hospitals Complem, Ile-Ife by the Management Board.
Who is the current chief medical director of Oauthc?
Professor Olusanya ADEJUYIGBE was born on August 4th 1952. at Akure, Ondo State, Nigeria. He attended the famous Oyemekun Grammer School, Akure from January 1964 to December 1968. He later attended University of Ibadan where he bagged Bachelor of Medicine, Bachelor of Surgery in the year 1975.
What is the name of the Chief medical Director of Oauthc?
The Chief Medical Director (CMD) of the Obafemi Awolowo University Teaching Hospital (OAUTH), Victor Adetiloye, has narrated how a 101-year-old woman survived COVID-19 in Osun State.
Why is CBC-MAC insecure?
1 Answer. In its plain form, CBC-MAC is vulnerable to “length extension attack”, where you just add some blocks at the end. So in order to stop people from doing that, you need to somehow mark the final block as indeed the final block. And not treat it like any other block.
What is AES XCBC?
AES-XCBC-MAC-96 is used as an authentication mechanism within the context of the IPsec Encapsulating Security Payload (ESP) and the Authentication Header (AH) protocols. For further information on ESP, refer to [ESP] and [ROADMAP].
What is AES block size?
AES uses a 128-bit block size, in which data is divided into a four-by-four array containing 16 bytes. Since there are eight bits per byte, the total in each block is 128 bits.
Where can I get CMAC?
- Click on the Start menu in the bottom-left corner of your computer. …
- Type ipconfig /all (note the space between the g and /).
- The MAC address is listed as series of 12 digits, listed as the Physical Address (00:1A:C2:7B:00:47, for example).