What is encapsulating security payload
Encapsulating Security Payload (ESP) is a member of the Internet Protocol Security (IPsec) set of protocols that encrypt and authenticate the packets of data between computers using a Virtual Private Network (VPN). … The enhanced version of IPsec in use is an Internet-layer security protocol.
What do you mean by encapsulating security payload?
Encapsulating Security Payload (ESP) is a member of the Internet Protocol Security (IPsec) set of protocols that encrypt and authenticate the packets of data between computers using a Virtual Private Network (VPN). … The enhanced version of IPsec in use is an Internet-layer security protocol.
What is encapsulation in cyber security?
Encapsulation refers to a programming approach that revolves around data and functions contained, or encapsulated, within a set of operating instructions. … Without strong and clearly defined boundaries between control spheres, attackers can gain unauthorized access to data and functions.
Where is encapsulating security payload used?
Encapsulated Security Payload (ESP) is used to provide security services in IPv4 and IPv6. It can be used alone or in unison with an AH. It can provide either confidentiality (i.e., encryption) or integrity protection (i.e., authentication), or both.What is the role of encapsulating security payload ESP of IPSec during data transmission?
ESP gives both authentication and encryption to the data packets. It provides multiple security services to give privacy, source authentication and content integrity to the packet. …
What is ESP 50?
ESP is IP Protocol 50, so is not based TCP or UDP protocols. … Transport mode encrypts the data payload, but maintains the original IP header fields. Tunnel mode encapsulates the whole packet, so encrypts both the header and payload, and adds its own header fields, treating the entire original packet as payload.
What is the difference between AH and ESP?
The AH protocol provides a mechanism for authentication only. … The ESP protocol provides data confidentiality (encryption) and authentication (data integrity, data origin authentication, and replay protection). ESP can be used with confidentiality only, authentication only, or both confidentiality and authentication.
Does ESP provide data integrity?
The ESP protocol provides data confidentiality (encryption) and authentication (data integrity, data origin authentication, and replay protection). … Either protocol can be used alone to protect an IP packet, or both protocols can be applied together to the same IP packet.What encryption does ESP use?
ESP uses AES-CCM and AES-GCM to provide encryption and authentication. An authentication algorithm cannot be selected if one of these “combined” algorithms is chosen. ESP uses AES-GMAC (Galios Message Authentication Code) to provide authentication, but not encryption.
What is ah in networking?The Authentication Header (abbreviated as AH) is a security mechanism that aims to help with authenticating the origins of packets of data that are transmitted under IP conditions (also known as the datagrams).
Article first time published onWhat is encapsulation with example?
Encapsulation in Java is a process of wrapping code and data together into a single unit, for example, a capsule which is mixed of several medicines. … Now we can use setter and getter methods to set and get the data in it. The Java Bean class is the example of a fully encapsulated class.
Why is encapsulation used?
Encapsulation is used to hide the values or state of a structured data object inside a class, preventing direct access to them by clients in a way that could expose hidden implementation details or violate state invariance maintained by the methods.
What is PDU encapsulation?
Encapsulation or layering is the addition of Protocol Control Information (PCI) to a Protocol Data Unit (PDU) by a communications protocol. The encapsulation adds headers before the start of a PDU. Encapsulation of data (an SDU) by adding a header (the PCI) to form a Ptotocol Data Unit processed by a lower layer.
What is VPN encapsulation?
Encapsulation works by hiding data packets inside other packets, which in turn enables a VPN software to make data undetectable while browsing the Internet. It works as camouflage for data by making it unrecognizable as sensitive data in transit over the network.
What is IP security briefly describe IP security policy and ESP Encapsulating Security Payload?
The IP security (IPSec) is an Internet Engineering Task Force (IETF) standard suite of protocols between 2 communication points across the IP network that provide data authentication, integrity, and confidentiality. It also defines the encrypted, decrypted and authenticated packets.
What is payload in cryptography and network security?
In computer networking and telecommunications, when a transmission unit is sent from the source to the destination, it contains both a header and the actual data to be transmitted. This actual data is called the payload. … The payload is required by the destination client.
Which is more secure ESP or AH?
Its main difference with ESP is that AH also secures parts of the IP header of the packet (such as the source/destination addresses). ESP provides authentication, integrity, replay protection, and confidentiality of the data (it secures everything in the packet that follows the header).
Does Ah provide encryption?
AH provides data integrity by using an authentication algorithm. It does not encrypt the packet.
What is IPsec tunnel?
An Internet Protocol Security (IPSec) tunnel is a set of standards and protocols originally developed by the Internet Engineering Task Force (IETF) to support secure communication as packets of information are transported from an IP address across network boundaries and vice versa.
What does IPSec stand for?
IPSEC stands for IP Security. It is an Internet Engineering Task Force (IETF) standard suite of protocols between 2 communication points across the IP network that provide data authentication, integrity, and confidentiality.
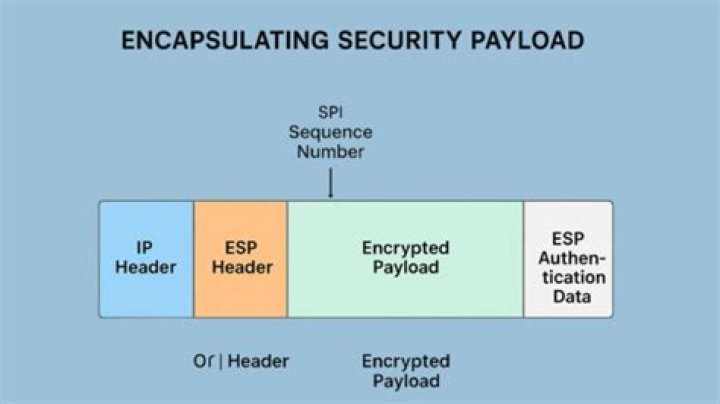
How many fields are available in encapsulating security payload?
As its name suggests, the ESP trailer comes after the data payload, and consists of three fields: padding, padding length, and the next header.
Can esp be fragmented?
The packet is post fragmented, meaning after encryption and encapsulation the packet size will be more than 1500 bytes, which will be more than the MTU size of a normal ethernet interface; hence the ESP packet will be fragmented.
What is encrypted payload?
MQTT Payload encryption is the encryption of application-specific data on the application level (typically, the MQTT PUBLISH packet payload or the CONNECT LWT payload). This approach allows end-to-end encryption of application data even on untrusted environments.
Which is better IPSec or OpenVPN?
IPSec with IKEv2 should in theory be the faster than OpenVPN due to user-mode encryption in OpenVPN however it depends on many variables specific to the connection. In most cases it is faster than OpenVPN. … Most customers report higher speeds than OpenVPN.
How Encapsulating Security Payload ESP works in tunnel and transport modes?
The Encapsulating Security Payload (ESP) operates in Transport Mode or Tunnel Mode. In Tunnel Mode, ESP encrypts the data and the IP header information. The Internet Security (IPsec) protocol uses ESP and Authentication Header (AH) to secure data as it travels over the Internet in packets.
What element of security is ensured by data confidentiality?
Confidentiality means that data, objects and resources are protected from unauthorized viewing and other access. Integrity means that data is protected from unauthorized changes to ensure that it is reliable and correct.
Why does ESP include Padding field?
Why does ESP include a padding field? … The ESP format requires that the Pad Length and Next Header fields be right aligned within a 32-bit word. Equivalently, the ciphertext must be an integer multiple of 32 bits. The Padding field is used to assure this alignment.
What is SPI in ESP header?
Security Parameter Index (SPI): Security Parameter Index (SPI) field in the Encapsulating Security Payload (ESP) header along with the destination address, and the IPsec protocol are used to uniquely identify the SA that applies to this packet.
What is header in network security?
An Authentication Header or AH is a security mechanism used in authenticating the origins of datagrams (packets of data transmitted under Internet Protocol or IP conditions), and in guaranteeing the integrity of the information that’s being sent.
What is header in cryptography?
The Authentication Header (AH) protocol provides data origin authentication, data integrity, and replay protection. … To ensure data origin authentication, AH includes a secret shared key in the algorithm that it uses for authentication. To ensure replay protection, AH uses a sequence number field within the AH header.
What protocol number is UDP?
DecimalKeywordProtocol17UDPUser Datagram18MUXMultiplexing19DCN-MEASDCN Measurement Subsystems20HMPHost Monitoring