What is Owasp in cyber security
The Open Web Application Security Project (OWASP) is a non-profit foundation dedicated to improving the security of software. … A guiding principle of OWASP is that all materials and information are free and easily accessed on their website, for everyone.
What is Owasp technology?
The Open Web Application Security Project (OWASP) is an online community that produces freely-available articles, methodologies, documentation, tools, and technologies in the field of web application security. The Open Web Application Security Project (OWASP) provides free and open resources.
Why is Owasp important?
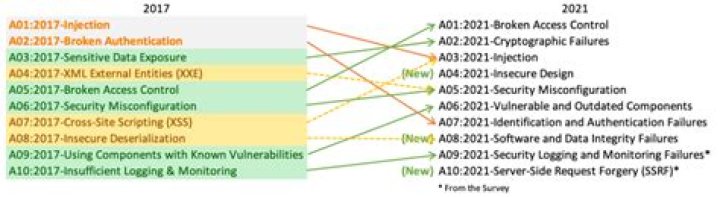
The OWASP Top 10 is important because it gives organisations a priority over which risks to focus on and helps them understand, identify, mitigate, and fix vulnerabilities in their technology. Each identified risk is prioritised according to prevalence, detectability, impact and exploitability.
How does Owasp work?
The OWASP Dependency-Check uses a variety of analyzers to build a list of Common Platform Enumeration (CPE) entries. CPE is a structured naming scheme, which includes a method for checking names against a system.What is Owasp testing?
OWASP pen testing describes the assessment of web applications to identify vulnerabilities outlined in the OWASP Top Ten. An OWASP pen test is designed to identify, safely exploit and help address these vulnerabilities so that any weaknesses discovered can be quickly addressed.
How is Owasp ranked 10?
RankSurvey Vulnerability CategoriesScore1Exposure of Private Information (‘Privacy Violation’) [CWE-359]7482Cryptographic Failures [CWE-310/311/312/326/327]584
Which vulnerabilities are part of Owasp?
- Injection. Injection occurs when an attacker exploits insecure code to insert (or inject) their own code into a program. …
- Broken Authentication. …
- Sensitive Data Exposure. …
- XML External Entities. …
- Broken Access Control. …
- Security Misconfiguration. …
- Cross-Site Scripting. …
- Insecure Deserialization.
What are cyber security vulnerabilities?
In cybersecurity, a vulnerability is a weakness that can be exploited by cybercriminals to gain unauthorized access to a computer system. After exploiting a vulnerability, a cyberattack can run malicious code, install malware and even steal sensitive data.What are the different types of vulnerabilities in cyber security?
- System Misconfigurations. …
- Out-of-date or Unpatched Software. …
- Missing or Weak Authorization Credentials. …
- Malicious Insider Threats. …
- Missing or Poor Data Encryption. …
- Zero-day Vulnerabilities. …
- Vulnerability Detection. …
- Cyber Security Vulnerability Assessment.
Some common SQL injection examples include: Retrieving hidden data, where you can modify an SQL query to return additional results. Subverting application logic, where you can change a query to interfere with the application’s logic. UNION attacks, where you can retrieve data from different database tables.
Article first time published onWhat are the three 3 types of network service vulnerabilities?
At the broadest level, network vulnerabilities fall into three categories: hardware-based, software-based, and human-based.
What do you mean by malware?
Malware is intrusive software that is designed to damage and destroy computers and computer systems. Malware is a contraction for “malicious software.” Examples of common malware includes viruses, worms, Trojan viruses, spyware, adware, and ransomware.
What is payload in cyber security?
In computer security, the payload is the part of the private user text which could also contain malware such as worms or viruses which performs the malicious action; deleting data, sending spam or encrypting data.
What is meant by zero day vulnerability?
A zero-day vulnerability is a vulnerability in a system or device that has been disclosed but is not yet patched. An exploit that attacks a zero-day vulnerability is called a zero-day exploit. … Vulnerable systems are exposed until a patch is issued by the vendor.
What does 1 mean in SQL?
WHERE 1 is a synonym for “true” or “everything.” It’s a shortcut so they don’t have to remove the where clause from the generated SQL.
What is HTML injection?
Hypertext Markup Language (HTML) injection is a technique used to take advantage of non-validated input to modify a web page presented by a web application to its users. … When applications fail to validate user data, an attacker can send HTML-fomatted text to modify site content that gets presented to other users.
What is single quote in SQL injection?
Single Quotes in SQL Injections. … For instance, in the SQL query context, single and double quotes are used as string delimiters. They are used both at the beginning and the end of a string. This is why when a single or double quote is injected into a query, the query breaks and throws an error.
Who uses Owasp?
For nearly two decades corporations, foundations, developers, and volunteers have supported the OWASP Foundation and its work.
Is Owasp a security framework?
The OWASP Security Knowledge Framework is an open source web application that explains secure coding principles in multiple programming languages. The goal of OWASP-SKF is to help you learn and integrate security by design in your software development and build applications that are secure by design.
What is Owasp compliance?
The OWASP Application Security Verification Standard (ASVS) Project provides a basis for testing web application technical security controls and also provides developers with a list of requirements for secure development. … This standard can be used to establish a level of confidence in the security of Web applications.
What is the difference between network security and cyber security?
Under this view, cybersecurity is a subset of information security that deals with protecting an organization’s internet-connected systems from potential cyberattacks; and network security is a subset of cybersecurity that is focused on protecting an organization’s IT infrastructure from online threats.
Which form of encryption does WPA use?
WPA uses TKIP and WPA2 uses the AES algorithm.
What are the 6 types of malware?
- Virus. Viruses are designed to damage the target computer or device by corrupting data, reformatting your hard disk, or completely shutting down your system. …
- Worm. …
- Trojan Horse. …
- Spyware. …
- Adware. …
- Ransomware.
What is a Trojan hack?
Trojans can use the victim computer to attack other systems using Denial of Services. … Trojans can encrypt all your files and the hacker may thereafter demand money to decrypt them. These are Ransomware Trojans. They can use your phones to send SMS to third parties.
What is the example of MCAfee?
Que.MCAfee is an example ofb.Quick Healc.Antivirusd.Photo Editing SoftwareAnswer:Antivirus
Is Macro A virus?
A macro virus is a computer virus written in the same macro language as the software it infects — common victims include Microsoft Excel and Word. Because they target software rather than systems, macro viruses can infect any operating system. So a macro virus can infect a PC or Mac.
What is another word for payload?
loadcargohaulfreightburdenladingweightdraughtUKdraftUSloading
Why is it called a payload?
Payload (n.) also pay-load, 1917, from pay + load (n.). Originally the part of a truck’s (later an aircraft’s) load from which revenue is derived (passengers, cargo, mail); figurative sense of “bombs, etc. carried by a plane or missile” is from 1936.