What is port scan attack
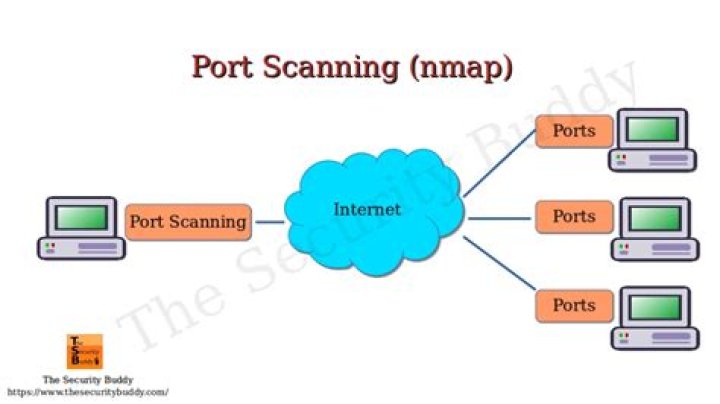
A port scan is a common technique hackers use to discover open doors or weak points in a network. A port scan attack helps cyber criminals find open ports and figure out whether they are receiving or sending data. It can also reveal whether active security devices like firewalls are being used by an organization.
How do I stop port scan attacks?
Install a Firewall: A firewall can help prevent unauthorized access to your private network. It controls the ports that are exposed and their visibility. Firewalls can also detect a port scan in progress and shut them down.
How is port scanning attacks detected?
Network scanning involves detecting all active hosts on a network and mapping them to their IP addresses. Port scanning refers to the process of sending packets to specific ports on a host and analyzing the responses to learn details about its running services or locate potential vulnerabilities.
Should I be worried about a port scan?
How Dangerous Are Port Scans? A port scan can help an attacker find a weak point to attack and break into a computer system. It’s only the first step, though. Just because you’ve found an open port doesn’t mean you can attack it.Is a port scan illegal?
In the U.S., no federal law exists to ban port scanning. … However – while not explicitly illegal – port and vulnerability scanning without permission can get you into trouble: Civil lawsuits – The owner of a scanned system can sue the person who performed the scan.
How long does a full port scan take?
Typical scan times A default full scan of 2000-4000 assets takes 2-3 days. An offboard QRadar Vulnerability Manager processor on a managed host (600) is required when more than 50,000 assets are being scanned regularly or when scans are running for long periods of time on the QRadar Console.
Why do hackers use port scanning?
A port scan is a common technique hackers use to discover open doors or weak points in a network. A port scan attack helps cyber criminals find open ports and figure out whether they are receiving or sending data. It can also reveal whether active security devices like firewalls are being used by an organization.
Is port scanning intrusive?
Nonintrusive methods generally include a simple scan of the target system’s attributes (e.g., inspecting the file system for specific files or file versions, checking the registry for specific values, scanning for missing security updates, port scanning to discover which services are listening). …Why are ports filtered?
A filter port indicates that a firewall, filter, or other network issue is blocking the port. Some standard services that can create a filter port can be, but not limited to, a server or network firewall, router, or security device. A common tool that is used to check the status of ports is Nmap.
What is aggressive scan?Aggressive mode enables OS detection ( -O ), version detection ( -sV ), script scanning ( -sC ), and traceroute ( –traceroute ). This mode sends a lot more probes, and it is more likely to be detected, but provides a lot of valuable host information.
Article first time published onIs forwarding a port safe?
Port Forwarding is not that risky because it relies on your network safety and the targeted ports that you are using. The whole process is actually safe as long as you have a security firewall or a VPN connection on your computer or network.
Is Angry IP Scanner safe?
Is Angry IP Scanner safe? Angry IP Scanner is safe to use. The utility is just a monitor and doesn’t have the power to make any changes to your device settings. The information that the service returns is simply a list of IP addresses that are in use, with any gaps in a range implying IP addresses that are unused.
What ports do hackers use?
Port NumberProtocol[s]Port Service161TCP, UDPSNMP [Simple Network Management Protocol]443TCPHTTPS [HTTP over TLS]512-514TCPBarkley r-services and r-commands [e.g., rlogin, rsh, rexec]1433TCP, UDPMicrosoft SQL Server [ms-sql-s]
What can hackers do with open ports?
Malicious (“black hat”) hackers (or crackers) commonly use port scanning software to find which ports are “open” (unfiltered) in a given computer, and whether or not an actual service is listening on that port. They can then attempt to exploit potential vulnerabilities in any services they find.
What is popular IP and port scanner?
_____________ is a popular IP address and port scanner. Explanation: Angry IP scanner is a light-weight, cross-platform IP and port scanning tool that scans a range of IP. It uses the concept of multithreading for making fast efficient scanning.
How long does it take to scan 65535 ports?
In the Protocol field, select a protocol. The default values are TCP & UDP. Note: UDP port scans are much slower than TCP port scans because of the way that UDP works. A UDP port scan can take up to 24 hours to scan all ports (1-65535) on an asset.
What is aggressive scan in Nmap?
Aggressive Scanning Nmap has an aggressive mode that enables OS detection, version detection, script scanning, and traceroute. … However, an aggressive scan also sends out more probes, and it is more likely to be detected during security audits.
Why Nmap takes too long?
By default, Nmap scans the most common 1,000 ports. On a fast network of responsive machines, this may take a fraction of a second per host. But Nmap must slow down dramatically when it encounters rate limiting or firewalls that drop probe packets without responding. UDP scans can be agonizingly slow for these reasons.
Is port blocked?
The best way to check if a port is blocked is to do a port scan from the client machine. Using a PortScan utility you will get one of 3 results. telnet is another command line option that is usually installed on the OS by default.
Can you exploit filtered ports?
tl;dr No, you won’t be able to directly exploit this vulnerability through a filtered port, and it can’t be detected in this way.
What is unfiltered port?
LBV Unfiltered is aged in large wooden vats and then drawn off into bottle with no fining or filtration. … Late Bottled Vintage is bottled when ready to drink. This Port benefits from being decanted before serving, as it is not filtered when bottled.
Which method of port scanning is the most popular?
Port Scanning Protocols The most commonly used method of TCP scanning is synchronized acknowledged (SYN) scans. SYN scanning involves creating a partial connection to the host on the target port by sending a SYN packet and then evaluating the response from the host.
Why do many organizations ban port scanning activities on their internal networks?
Many organizations ban port scanning on their internal networks because this could be an easy way for a hacker to footprint a large number of computers quickly. Also, port scanning takes up un-necessary system and network resources.
What are the types of port scanning?
- PING SCAN. Ping Scans are used to sweep a whole network block or a single target to check to see if the target is alive. …
- TCP Half-Open. This is probably the most common type of port scan. …
- TCP CONNECT. …
- UDP. …
- STEALTH SCANNING – NULL, FIN, X-MAS.
What is an Nmap switch?
This switch lets you specify single ports, ranges, or lists of ports to scan. You can also specify whether you want to ping UDP or TCP ports only. For example, to scan TCP ports 23 (Telnet), 25 (SMTP), and 80 (HTTP), you can type this: NMap -p T:23,25,80.
What is Nmap Zenmap?
Zenmap is the Nmap security scanner graphical user interface and provides for hundreds of options. It lets users do things like save scans and compare them, view network topology maps, view displays of ports running on a host or all hosts on a network, and store scans in a searchable database.
Why are null FIN and Xmas scans generally used?
The NULL, FIN, and Xmas scans clear the SYN bit and thus fly right through those rules. Another advantage is that these scan types are a little more stealthy than even a SYN scan. Don’t count on this though—most modern IDS products can be configured to detect them.
What happens if you forward port 80?
The client listens on a random port above 1024 for the server responses. So having port 80 forwarded to the raspberry, will not affect other PCs in the network when using the network regulary. Of course you can only forward the port to one PC in your home network, so you can only run one raspberry-server at a time.
Does port forwarding affect other devices?
Short answer: no. Forwarding a a fixed number of ports from your router to a specific device/pc on your network will not impact the connectivity of that PC or other devices. Now, if you forward the entire port range (1–65535) to a single device, it might be an issue.
Is there an alternative to port forwarding?
1 Answer. There are no Home/SOHO alternatives to Port Forwarding, per se, but it is not always necessary to manually administer port forwarding rules. There is also a means to bypass the need for port forwarding via the Reverse Tunneling technique, using VPN or SSH tunnels.
Is Angry IP Scanner malware?
Important: There are no trojans or viruses in Angry IP Scanner’s ipscan.exe. … Some antivirus software vendors (McAfee, Symantec, and some others) are identifying Angry IP Scanner as ‘potentially unwanted program’ or risky ‘hacktool’. Their programs often delete Angry IP Scanner from the disk during virus scanning.