Are OAuth tokens encrypted
OAuth 2.0, on the other hand, has six flows for different types of applications and requirements, and enables signed secrets over HTTPS. OAuth tokens no longer need to be encrypted on the endpoints in 2.0 since they are encrypted in transit.
Are access tokens encrypted?
JWT-based access tokens can be encrypted by using RFC 7516 (JSON Web Encryption).
Where are OAuth tokens stored?
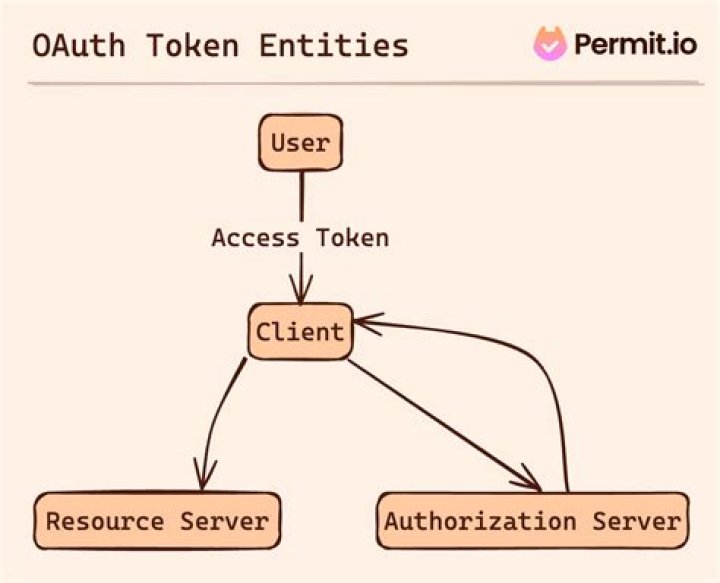
Tokens received from OAuth providers are stored in a Client Access Token Store. You can configure client access token stores under the Libraries > OAuth2 Stores node in the Policy Studio tree view.
Can OAuth token be stolen?
Adversaries can steal user application access tokens as a means of acquiring credentials to access remote systems and resources. … Adversaries can leverage OAuth authorization by constructing a malicious application designed to be granted access to resources with the target user’s OAuth token.Where are OAuth access tokens stored?
The client, in OAuth terminology, is the component that makes requests to the resource server, in your case, the client is the server of a web application (NOT the browser). Therefore, the access token should be stored on the web application server only.
Can someone else use my token?
The security token always generates a random code for every transaction thereby making it impossible for another person to carry out online transactions from your account. There is no need to visit a branch.
What happens if someone steals your refresh token?
If the refresh token can be stolen, then so can the access token. With such an access token, the attacker can start making API calls. To make matters even more complicated, access tokens are often self-contained JWT tokens. Such tokens contain all the information needed for the API to make security decisions.
Is it safe to store access token in database?
5 Answers. Technically you can store the access token in your database, and use it for API calls until it expires. It might be more trouble than its worth, though.Can JWT be decoded?
A valid JWT can consist of just the header and payload sections. … By design, anyone can decode a JWT and read the contents of the header and payload sections. But we need access to the secret key used to create the signature to verify a token’s integrity.
Should token be store in database?4 Answers. If you are using a Token base Authentication as described in the linked/mentioned web page there is no necessarity to store the token in a database.
Article first time published onIs it safe to store access token in local storage?
Local storage is vulnerable because it’s easily accessible using JavaScript and an attacker can retrieve your access token and use it later. However, while httpOnly cookies are not accessible using JavaScript, this doesn’t mean that by using cookies, you are safe from XSS attacks involving your access token.
Is it safe to store token in cookie?
With cookies, the access token is still hidden, attackers could only carry out “onsite” attacks. The malicious scripts injected into the web app could be limited, or it might not be very easy to change/inject more scripts. Users or web apps might need to be targeted first by attackers.
What is token authentication?
Token-based authentication is just one of many web authentication methods used to create a more secure verification process. … Token authentication requires users to obtain a computer-generated code (or token) before they’re granted network entry.
How can I store oauth tokens in database?
1 Answer. A solution for this is to encrypt the data before is saved into the database and decrypt it each time you need to access it. In your case I think that symmetric encryption is the correct choice, thus you will need to have a private key that must be kept safe at all times.
Should refresh tokens be encrypted?
The Refresh Token, when paired with the Client ID and Secret can be used to generate a new Access Token. It should be securely stored and encrypted. You should only store those tokens that are necessary for your application to function alongside your codebase.
Is JSON Web Token Secure?
JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. This information can be verified and trusted because it is digitally signed.
Why are refresh tokens more secure?
The reason for that is the sensitivity of this piece of information. You can think of it as user credentials, since a Refresh Token allows a user to remain authenticated essentially forever. Therefore you cannot have this information in a browser, it must be stored securely.
Can token be shared?
There are different ways in which such token can be shared: The same token can be reused. A different token can be embedded in the original token. The original token can be exchanged.
How do secure tokens work?
Security tokens authenticate identities electronically by storing personal information. They are issued by Security Token Services (STS), which authenticate the person’s identity. They may be used in place of or in addition to a password to prove the owner’s identity.
Does GTB token expire?
Hi, Token does not expire but can get damaged if not properly handled.
Can you decode JWT without secret?
7 Answers. JWTs can be either signed, encrypted or both. If a token is signed, but not encrypted, everyone can read its contents, but when you don’t know the private key, you can’t change it.
Can we decode JWT token without?
I created a token with the private key by JWT, but when I try to decode it on I found that the token can be decoded without any key given.
Is JWT the same as OAuth?
Basically, JWT is a token format. OAuth is an standardised authorization protocol that can use JWT as a token. OAuth uses server-side and client-side storage. If you want to do real logout you must go with OAuth2.
How long do OAuth tokens last?
By default, access tokens are valid for 60 days and programmatic refresh tokens are valid for a year. The member must reauthorize your application when refresh tokens expire.
Is OAuth cookie based?
One solution for this is, passing part of the access token via Authorization header and pass the other part via a Cookie. …
Where JWT token is stored?
A JWT needs to be stored in a safe place inside the user’s browser. If you store it inside localStorage, it’s accessible by any script inside your page.
What is an OAuth access token?
OAuth Access Tokens An OAuth Access Token is a string that the OAuth client uses to make requests to the resource server. … Access tokens do not convey user identity or any other information about the user to the OAuth client. Access tokens should only be used to make requests to the resource server.
Where should I store the access token?
Therefore, the access token should be stored on the web application server only. It should not be exposed to the browser, and it doesn’t need to, because the browser never makes any direct requests to the resource server.
Is SessionStorage more secure than LocalStorage?
SessionStorage based on your use-case. If your application needs data to be shared across multiple browser windows and tabs, use the LocalStorage otherwise, use the SessionStorage. Both SessionStorage and LocalStorage are vulnerable to XSS attacks. Therefore avoid storing sensitive data in browser storage.
Is LocalStorage more secure than cookies?
Although cookies still have some vulnerabilities, it’s preferable compared to localStorage whenever possible. … Both localStorage and cookies are vulnerable to XSS attacks, but it’s harder for the attacker to do the attack when you’re using httpOnly cookies.
How do I protect my local storage data?
serving all content (when online) from a single trusted server over ssl. validating all data going to and from local storage on the server using owasp antisamy project. in the network section of the appcache, not using *, and instead listing only the URIs required for connection with the trusted server.