What is the impact of security misconfiguration
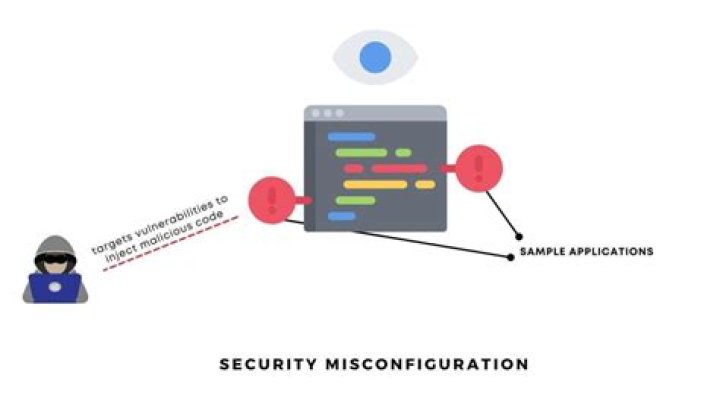
Security misconfiguration flaws give attackers unauthorized access to system data and functionality. Occasionally, such flaws can lead to severe consequences; for example, a complete system compromise. The business impact can be great or small depending on the protection needs of the application and data.
Why is security misconfiguration bad?
Misconfigured security can stem from very simple oversights, but can leave an application wide open to attackers. In some cases, misconfiguration can leave data exposed without any need for an active attack by malicious agents. … The more data and code exposed to users, the greater the risk for app security.
What is an example of security misconfiguration?
Some examples of security misconfigurations include insecure default configurations, incomplete or ad-hoc configurations, open cloud storage, misconfigured HTTP headers, unnecessary HTTP methods, overly permissive Cross-Origin resource sharing (CORS), and verbose error messages.
What is misconfiguration in security?
Security misconfigurations are security controls that are inaccurately configured or left insecure, putting your systems and data at risk. Basically, any poorly documented configuration changes, default settings, or a technical issue across any component in your endpoints could lead to a misconfiguration.Is Misconfiguration a threat or vulnerability?
While both threats can result in exploits and exposures, misconfigurations are incorrect settings made by the environment’s creator, not flaws in the system or code. Breaches caused by misconfigurations have resulted in hundreds of thousands of exposed records.
How is server misconfiguration prevented?
- Disable administration interfaces.
- Disable debugging.
- Disable use of default accounts/passwords.
- Configure server to prevent unauthorized access, directory listing, etc.
How security misconfiguration can compromise the security of a system?
These security misconfigurations can lead an attacker right into the system and result in a partially or even totally compromised system. Attackers find these misconfigurations through unauthorized access to default accounts, unused web pages, unpatched flaws, unprotected files and directories and more.
Is directory listing a security misconfiguration?
If Directory listing is not disabled on the server and if attacker discovers the same then the attacker can simply list directories to find any file and execute it. … If not removed from production server would result in compromising your server.What is the meaning of misconfiguration?
Filters. An incorrect or inappropriate configuration. noun.
What is security misconfiguration in Owasp?* Unnecessary features are enabled or installed (e.g. unnecessary ports, services, pages, accounts, or privileges). * Default accounts and their passwords still enabled and unchanged. * Error handling reveals stack traces or other overly informative error messages to users.
Article first time published onWhat is firewall misconfiguration?
Breach avenues: A firewall misconfiguration that results in unintended access can open the door to breaches, data loss and stolen or ransomed IP. Unplanned outages: A misconfiguration could prevent a customer from engaging with a business, and that downtime leads to lost revenues.
What is the impact of the incorrect configuration of a firewall in IT security?
Improper firewall configuration can result in attackers gaining unauthorized access to protected internal networks and resources.
Can detect misconfiguration such as leaky APIs?
testing (DAST) can detect misconfigurations, such as leaky APIs. Cross-site scripting (XSS) flaws give attackers the capability to inject client-side scripts into the application, for example, to redirect users to malicious websites.
Which of the following is a form of security misconfiguration?
Unencrypted files. Old and out of date web applications. Unsecured devices. Web application and cloud misconfiguration.
What is cloud Misconfiguration?
Cloud misconfiguration can be defined as any errors, glitches or gaps in your cloud environment that can leave you exposed to risk. This cloud security risk could come in the form of data breaches, cloud breaches, insider threats or external bad actors who leverage vulnerabilities to gain access to your network.
Is disfiguration a word?
noun The state of being disfigured; disfigurement; deformity.
What is the impact of an activated directory listing?
Exposing the contents of a directory can lead to an attacker gaining access to source code or providing useful information for the attacker to devise exploits, such as creation times of files or any information that may be encoded in file names. The directory listing may also compromise private or confidential data.
Is there any way of preventing configuration vulnerability?
Here are some ways that small and medium-sized businesses can prevent security configuration vulnerabilities: Update passwords regularly and use multi-factor authentication. Run security checks on third-party platforms. Ensure that all employees use the VPN if working remotely (not a random coffee shop’s WiFi -– gulp!)
Why is firewall misconfiguration The most common cause of firewall failure?
The most common cause of firewall failure is misconfiguration. … This means that a firewall has incorrect specifications because of user error, or lack of research. In fact, back in 2016, Gartner predicted that through 2020, this figure would rise to 99%.
Why are firewalls bad?
Any change to the firewall can negatively affect the network and the security. Changes to the firewall are frequent, because threats are constantly changing – which is where problems can arise. There are people in their basements who create threats all day long.
Why firewalls do not give full proof security?
Firewalls control both incoming and outgoing network traffic. They can allow certain packets to pass through or else disable access for them. … This simple example shows that a firewall cannot evaluate the contents of “legitimate” packets and can unknowingly pass through some attacks on the Web server.
What is the firewall security?
A firewall is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules. Firewalls have been a first line of defense in network security for over 25 years.
What happens if a firewall is not configured?
You need to set up your firewall so it’s restricting network traffic to only those authorized to access it. If a firewall isn’t properly configured, you might as well not have one. … It was through this vulnerability that the attacker accessed their network.
How implementing a DMZ can improve network security?
DMZ’s are an essential part of network security for both individual users and large organizations. They provides an extra layer of security to the computer network by restricting remote access to internal servers and information, which can be very damaging if breached.